If Your AI Agent Ran npm install During the Axios Attack, You're Compromised
A security proxy for AI coding agents, enforced at the OS level. Register your interest to be notified when we go live.
 esc to close
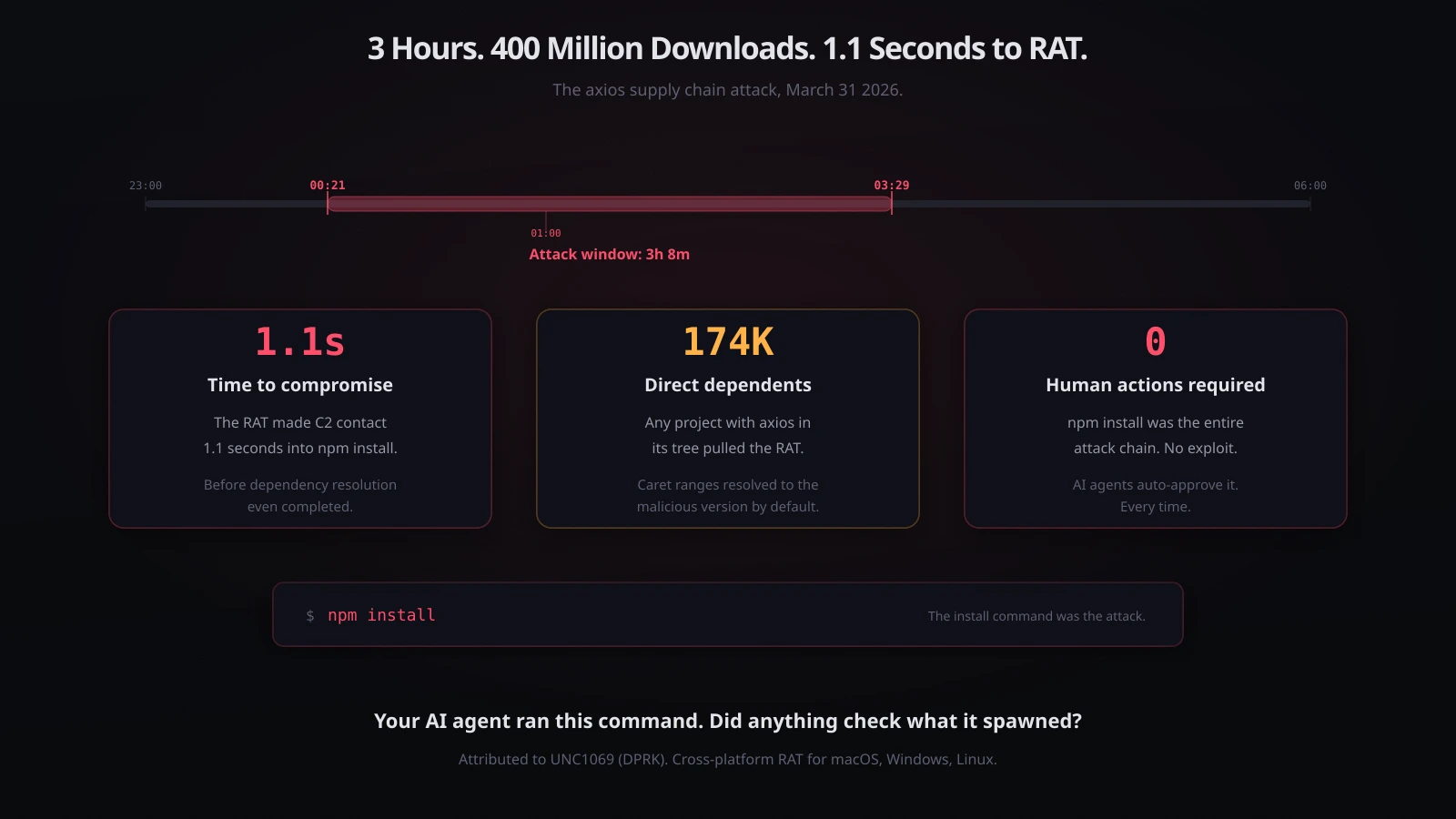
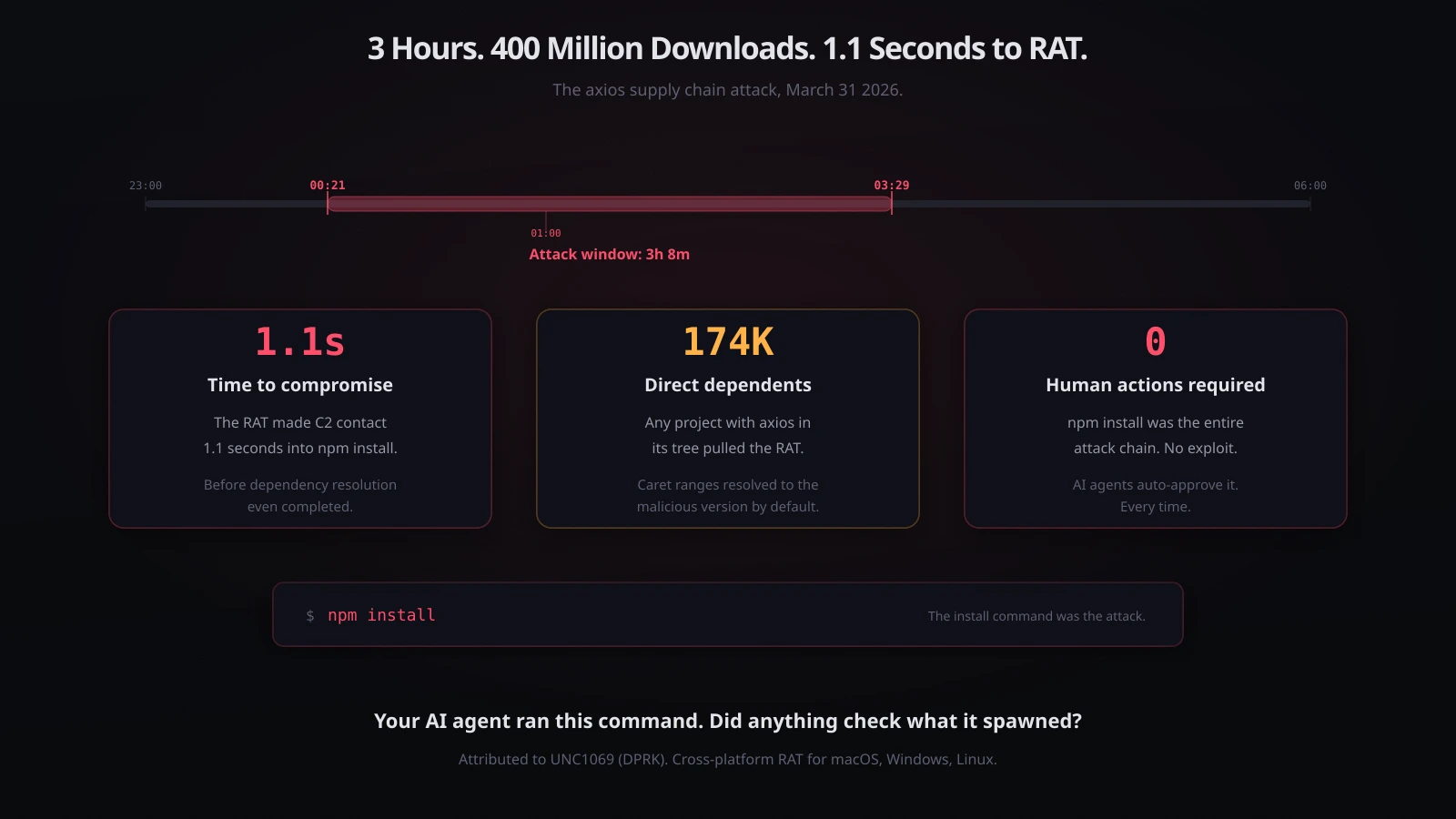
esc to closeAt 00:21 UTC on March 31, 2026, a DPRK-linked attacker published a backdoored version of axios to the npm registry. axios is one of the most depended-upon packages in the JavaScript ecosystem - 400 million monthly downloads, 174,000 direct dependents1. The malicious version included a postinstall hook that dropped a cross-platform Remote Access Trojan onto macOS, Windows, and Linux systems. The RAT executed 1.1 seconds into npm install, before dependency resolution even completed2.
The malicious versions were removed at 03:29 UTC. The window was 3 hours and 8 minutes.
During those 3 hours, every npm install that resolved a caret-range dependency on axios - which is the default for every project that depends on it - pulled version 1.14.1 and executed the RAT. No vulnerability was exploited. No user action was required beyond npm install. The install command was the attack.
AI coding agents run npm install constantly. It is one of their most common operations. They run it when setting up projects, adding dependencies, running builds, and resolving errors. They run it autonomously, without asking, because it is a routine operation that permission systems auto-approve.
If your AI coding agent ran npm install in any project that depends on axios during that 3-hour window, the RAT is on your machine.
What happened
The attacker compromised the npm account of jasonsaayman, the lead axios maintainer. The publishing email changed from the legitimate address to an anonymous ProtonMail account. Two versions were published: axios@1.14.1 (tagged latest) and axios@0.30.4 (tagged legacy), covering both the 1.x and 0.x branches13.
The attack was staged over 18 hours:
| Time (UTC) | Event |
|---|---|
| March 30, 05:57 | plain-crypto-js@4.2.0 published (clean decoy, establishing registry history) |
| March 30, 23:59 | plain-crypto-js@4.2.1 published (malicious payload added) |
| March 31, 00:21 | axios@1.14.1 published with plain-crypto-js as dependency |
| March 31, 01:00 | axios@0.30.4 published (covering the legacy branch) |
| March 31, 01:50 | GitHub Security Advisory filed |
| March 31, 03:15 | npm removes both axios versions |
| March 31, 03:29 | Malicious versions fully unpublished |
A critical forensic indicator: legitimate axios releases use GitHub Actions with npm's OIDC Trusted Publisher mechanism. The malicious versions were published via direct CLI without provenance attestations2. npm's registry accepted them anyway.
How the RAT works
The malicious plain-crypto-js@4.2.1 package contained a setup.js postinstall script with two-layer obfuscation - string reversal plus Base64, then XOR cipher. When decoded, it dropped platform-specific payloads13:
macOS: Downloads RAT to /Library/Caches/com.apple.act.mond, executes via AppleScript
Windows: Copies PowerShell to %PROGRAMDATA%\wt.exe, executes via VBScript
Linux: Downloads Python RAT to /tmp/ld.py
All three variants share an identical C2 protocol: 60-second beacon intervals to sfrclak.com:8000, with command support for kill, runscript, peinject, and rundir1. The macOS variant overlaps significantly with WAVESHAPER, a backdoor attributed to UNC1069, a DPRK-linked threat cluster1.
After deploying the payload, the dropper performed anti-forensics: it deleted setup.js, deleted the malicious package.json, and renamed a pre-staged clean stub (reporting version 4.2.0) to package.json. Post-infection, npm list shows plain-crypto-js@4.2.0 - the clean version - not the malicious 4.2.12.
StepSecurity captured the execution in a GitHub Actions environment. The C2 contact happened 1.1 seconds into npm install. A second connection from a detached nohup process (orphaned to PID 1) confirmed the stage-2 payload executed independently of the install process2. By the time npm install finished, the RAT was already running as a separate process.
Why AI agents made this worse
A developer running npm install manually might notice something odd - an unexpected dependency appearing, a postinstall script running, unusual network activity. They probably would not. But they at least have the opportunity.
An AI coding agent has no such opportunity. When Claude Code, Cursor, Cline, Codex, or any other AI coding agent decides to run npm install, it executes the command and moves on. The agent does not review postinstall scripts. It does not check for new transitive dependencies. It does not monitor network connections spawned by the install process. It runs the command because the command is routine, and routine commands are what agents are designed to handle without interruption.
 esc to close
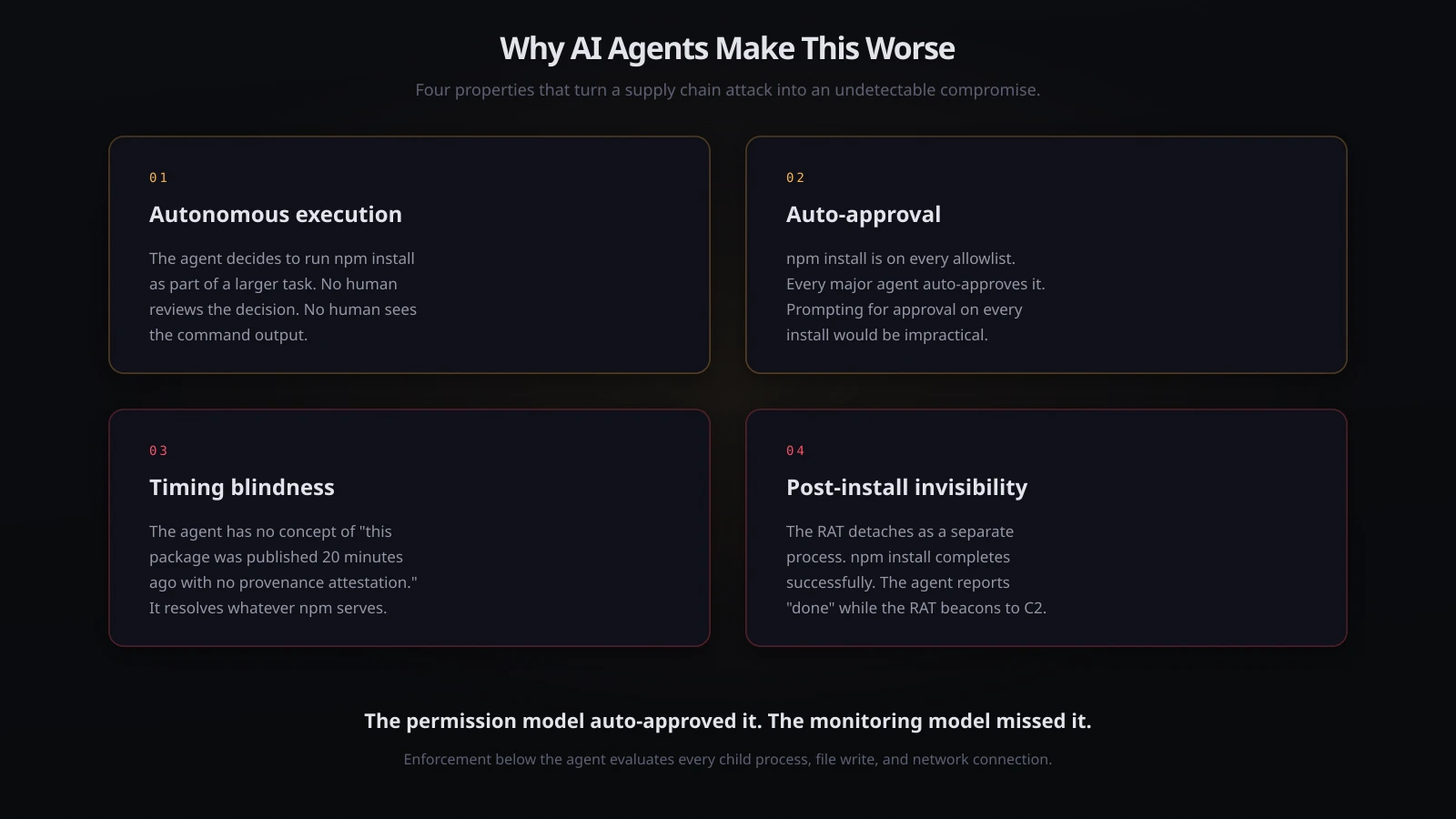
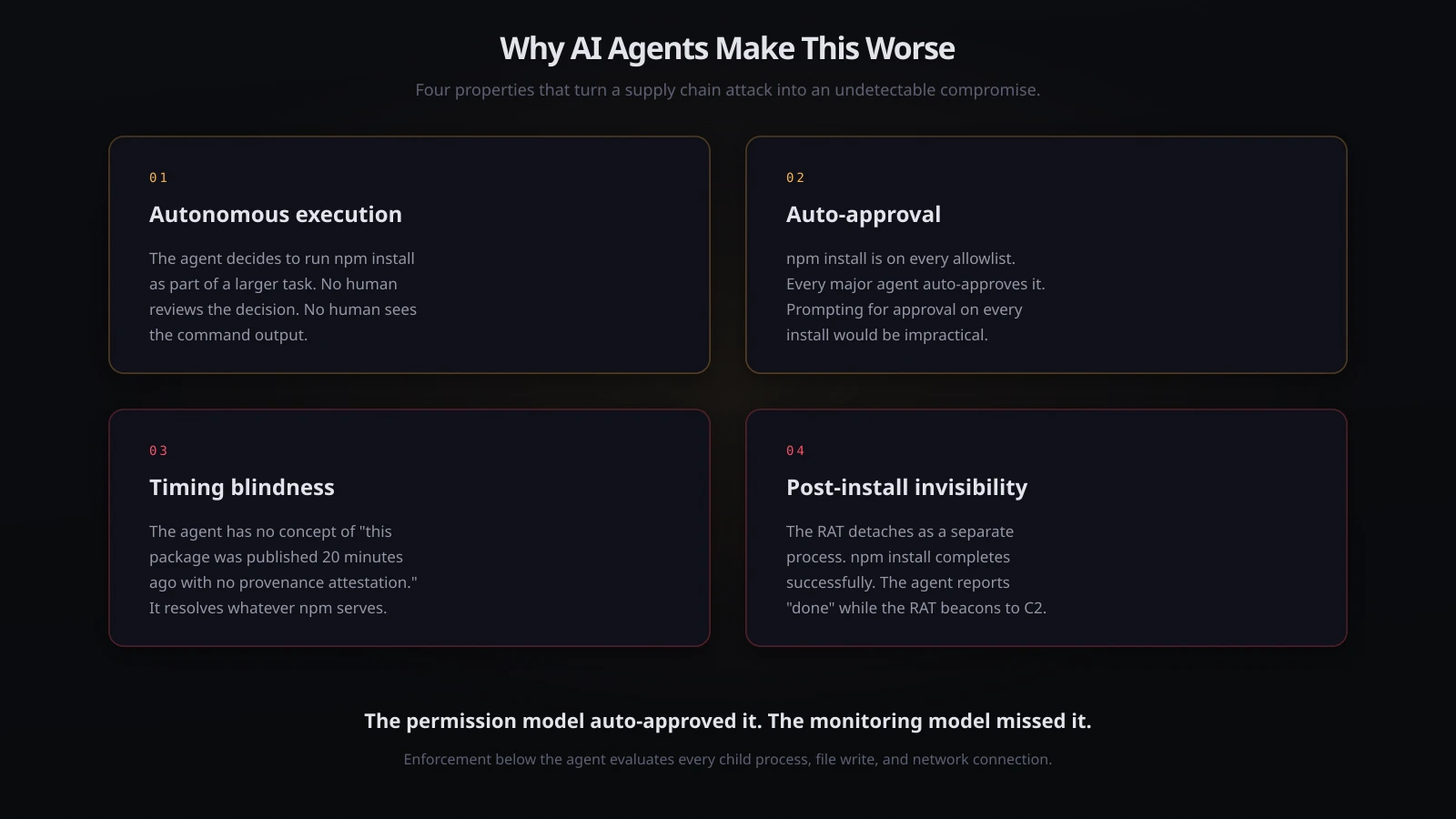
esc to closeThis is the pattern that makes supply chain attacks categorically more dangerous in the age of AI agents:
-
Autonomous execution. The agent decides to run
npm installas part of a larger task. No human reviews the decision. No human sees the command output. -
Auto-approval. Every major AI coding agent auto-approves
npm install. It is on every allowlist. It would be impractical to prompt for approval on every package install - agents run dozens per session. -
Timing blindness. The agent has no concept of "this package was published 20 minutes ago and has no provenance attestation." It resolves whatever version the registry serves.
-
Post-install invisibility. The RAT detaches as a separate process. The agent's command completes successfully. The agent reports "dependencies installed" and continues working. The RAT is already beaconing to C2.
A human developer who ran npm install during the attack window is compromised. An AI agent that ran it is compromised in exactly the same way, except nobody was watching.
The extraordinary timing
The axios attack happened on the same morning as the Claude Code source map leak - an unrelated incident where Anthropic accidentally shipped a 59.8MB source map in @anthropic-ai/claude-code@2.1.88, exposing the full TypeScript source to anyone who installed via npm45.
The two events were independent. But a developer who ran npm install @anthropic-ai/claude-code between 00:21 and 03:29 UTC got both: the leaked source code in their node_modules, and - if their project or any transitive dependency resolved axios - a DPRK RAT on their machine. Neither was detectable by Claude Code's own security checks, because both happened during the install, before the agent even ran.
Anthropic has since recommended the native installer (curl -fsSL https://claude.ai/install.sh | bash) as the primary installation method, specifically because it bypasses the npm dependency chain entirely5.
What to do right now
If you or your AI agent ran npm install in any JavaScript project between 00:21 and 03:29 UTC on March 31, 2026:
1. Check your lockfiles. Search package-lock.json, yarn.lock, or bun.lockb for axios@1.14.1, axios@0.30.4, or plain-crypto-js. If present, you are affected.
2. Check for RAT artifacts. Look for:
- macOS:
/Library/Caches/com.apple.act.mond - Windows:
%PROGRAMDATA%\wt.exe - Linux:
/tmp/ld.py
3. Check for C2 communication. Look for DNS resolution or connections to sfrclak.com (IP: 142.11.206.73:8000).
4. If affected, treat the machine as fully compromised. Rotate all credentials: npm tokens, SSH keys, cloud provider keys, CI/CD secrets, API tokens, database passwords. Everything accessible from the machine during and after the attack window.
5. Pin axios to safe versions. axios@1.14.0 and axios@0.30.3 are clean. Use exact version pinning, not caret ranges.
6. Consider --ignore-scripts in CI/CD. Running npm ci --ignore-scripts prevents postinstall hooks from executing. This breaks legitimate postinstall scripts but eliminates the attack vector entirely.
What this means for AI agent security
The axios attack is the clearest demonstration yet of why npm install is not a safe command to auto-approve.
Every AI coding agent treats it as routine. Every permission system allowlists it. And on March 31, the routine command delivered a state-sponsored RAT to every machine that ran it with axios in the dependency tree.
This is not a novel attack vector. Supply chain attacks via npm have been documented for years - event-stream in 2018, ua-parser-js in 2021, colors and faker in 2022. What is new is the execution context: autonomous agents running package installs without human review, at scale, around the clock, across thousands of developer machines.
The pattern is consistent: the agent runs a command that looks routine, the command has side effects that are invisible to the agent, and the damage happens before anyone can intervene. The permission prompt model does not help because npm install is always approved. The monitoring model does not help because the RAT detaches before the command returns.
Where enforcement has to be
npm install is a process spawn. The postinstall hook is a child process spawn. The C2 connection is a network syscall. The RAT binary write is a file syscall.
Every step of this attack chain is a system call that enforcement below the agent can evaluate before it executes.
grith intercepts at the syscall boundary. When an agent runs npm install, grith evaluates the resulting process tree - not just the top-level command, but every child process, every file write, every network connection spawned during execution:
- A postinstall script making an outbound connection to an unknown domain (
sfrclak.com:8000)? Destination reputation flags it. Auto-deny. - A postinstall script writing an executable to
/Library/Caches/or%PROGRAMDATA%? Path sensitivity analysis flags a binary write outside the project directory. Auto-deny. - A detached
nohupprocess spawned by a package install? Behavioural anomaly detection flags a background process spawned by a dependency installation. Auto-deny.
The install itself proceeds. The legitimate dependencies resolve. The RAT never executes because the postinstall hook's outbound connection and binary write are blocked before they complete.
The caveat is important: grith only sees what runs through it. If you run npm install manually in a terminal outside grith exec, grith is not watching. The protection applies when agents run through the enforcement layer: grith exec -- claude or grith exec -- cursor. That is the design - enforcement wraps the agent, not the entire system.
The axios attack is the scenario grith is built for. The agent runs a routine command. The command has invisible side effects. The enforcement layer evaluates the side effects before they execute, regardless of whether the command looked routine. One command to wrap any agent: grith exec -- <your-agent>.
Footnotes
-
Elastic Security Labs: Inside the Axios supply chain compromise - one RAT to rule them all ↩ ↩2 ↩3 ↩4 ↩5
-
StepSecurity: axios Compromised on npm - Malicious Versions Drop Remote Access Trojan ↩ ↩2 ↩3 ↩4
-
Snyk: Axios npm Package Compromised - Supply Chain Attack Delivers Cross-Platform RAT ↩ ↩2
-
VentureBeat: Claude Code's source code appears to have leaked ↩
-
Gizmodo: Source Code for Anthropic's Claude Code Leaks at the Exact Wrong Time ↩ ↩2
Like this post? Share it.